This morning Techcrunch published a report which detailed a now patched bug in Peloton’s API that could have revealed some users private data on Peloton. The bug was discovered, and reported to Peloton, by Jan Masters, a security researcher at Pen Test Partners. You can read Masters’ full writeup here.
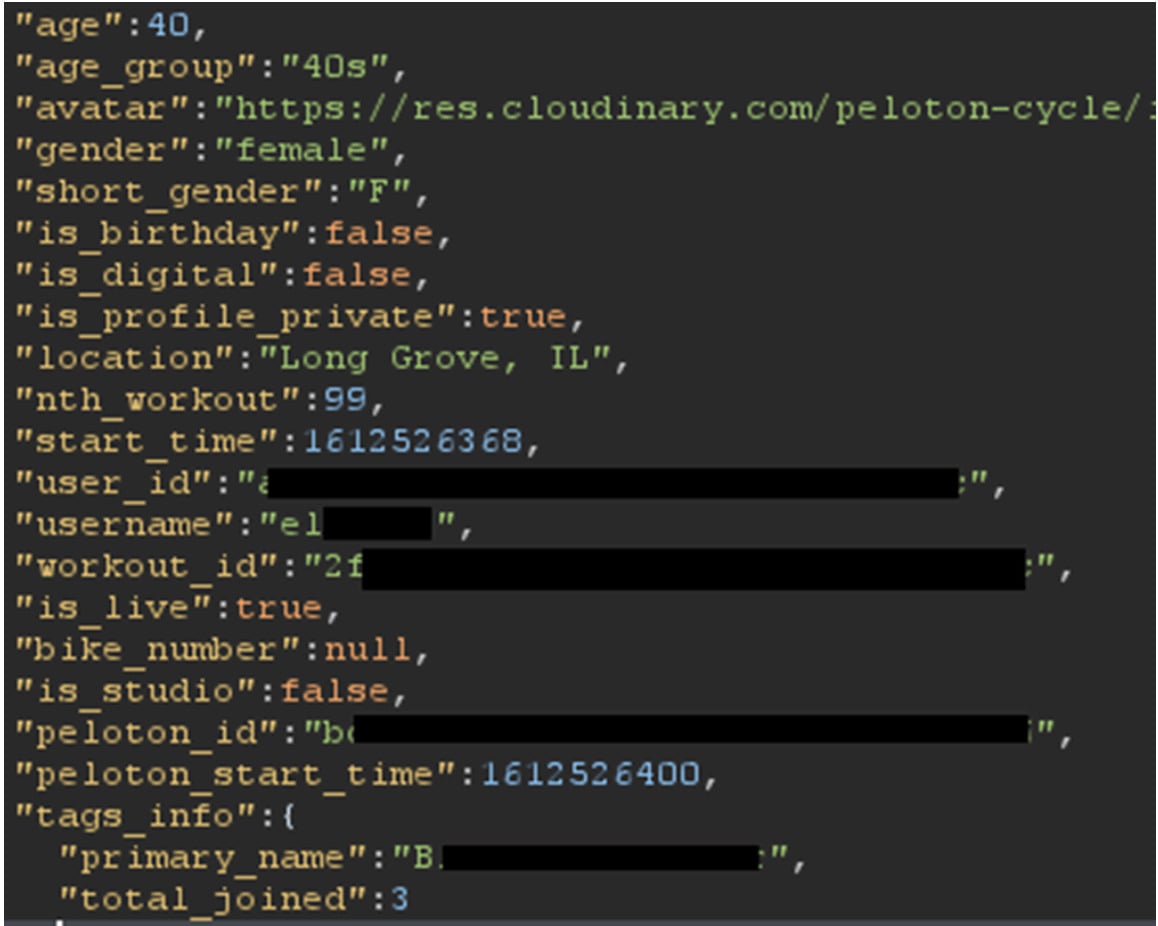
The bug in Peloton’s API allowed for the discovery of some profile information, even for profiles that were set to private. Information that was possible to find out included gender, city, weight, workout statistics, leaderboard tags, and more.
The bug had two main issues. First – the API calls to find out the data were unauthenticated, which meant you didn’t need a Peloton user account to discover them. This part of the issue was fixed within a week of being disclosed – but that meant the bug was still accessible to any of the 4.4+ million people with Peloton accounts.
The second part of the bug was that certain API calls were returning profile information for members, even if their profile was set to private. For example – a call to the workout details was returning the age, gender, location, primary leaderboard tag, if you were riding from home or in the studio, and if it was your birthday. This bug was left unpatched for more than 90 days after being disclosed.
Masters discovered the bug in January and reported it to Peloton. Peloton replied that they received the report, and two weeks later, made an update. However, the update left the vulnerability open, but restricted it to being only available to Peloton members. After 90 days, the bug was not fixed. At that point, Masters reached out to Techcrunch, who were able to get a dialog with Peloton going. Shortly after that the full bug was fixed.
Shortly after contact was made with the press office at Peloton we had contact direct from Peloton’s CISO, who was new in post.
The vulnerabilities were largely fixed within 7 days.
It’s a shame that our disclosure wasn’t responded to in a timely manner and also a shame that we had to involve a journalist in order to get listened to.
In fairness to Peloton they took it on the chin, thanked us, and acknowledged their failures in the process. I wish all vendors were so honest and grateful.
At this time it isn’t known of the bug was exploited:
But questions remain for Peloton. When asked repeatedly, the company declined to say why it had not responded to Masters’ vulnerability report. It’s also not known if anyone maliciously exploited the vulnerabilities, such as mass-scraping account data.
Support the site! Enjoy the news & guides we provide? Help us keep bringing you the news. Pelo Buddy is completely free, but you can help support the site with a one-time or monthly donation that will go to our writers, editors, and more. Find out more details here.
Get Our Newsletter Want to be sure to never miss any Peloton news? Sign up for our newsletter and get all the latest Peloton updates & Peloton rumors sent directly to your inbox.

All my peloton profile information is fake. People put real info in it? For what purpose?